 At Email Meter, we use Looker Studio to power our email statistics dashboards. Looker Studio is a modern BI & analytics platform used to tell stories with data.
To view your company’s email statistics dashboard in Looker Studio, users will need to be signed into a Google account.
With this guide, you will learn how to integrate Google with Microsoft Entra ID. After completing these steps, users will be able to sign-in to Email Meter with Google using their existing Microsoft SSO.
At Email Meter, we use Looker Studio to power our email statistics dashboards. Looker Studio is a modern BI & analytics platform used to tell stories with data.
To view your company’s email statistics dashboard in Looker Studio, users will need to be signed into a Google account.
With this guide, you will learn how to integrate Google with Microsoft Entra ID. After completing these steps, users will be able to sign-in to Email Meter with Google using their existing Microsoft SSO.
To follow this guide, you will need administrator permissions on both Microsoft and Google admin panels.
Requirements
To get started, you will need:- A Microsoft 365 subscription
- A Google Workspace tenant
Instructions
Create a SAML profile in Google Workspace
- Open a new tab in your browser, and sign in to the Google Admin.
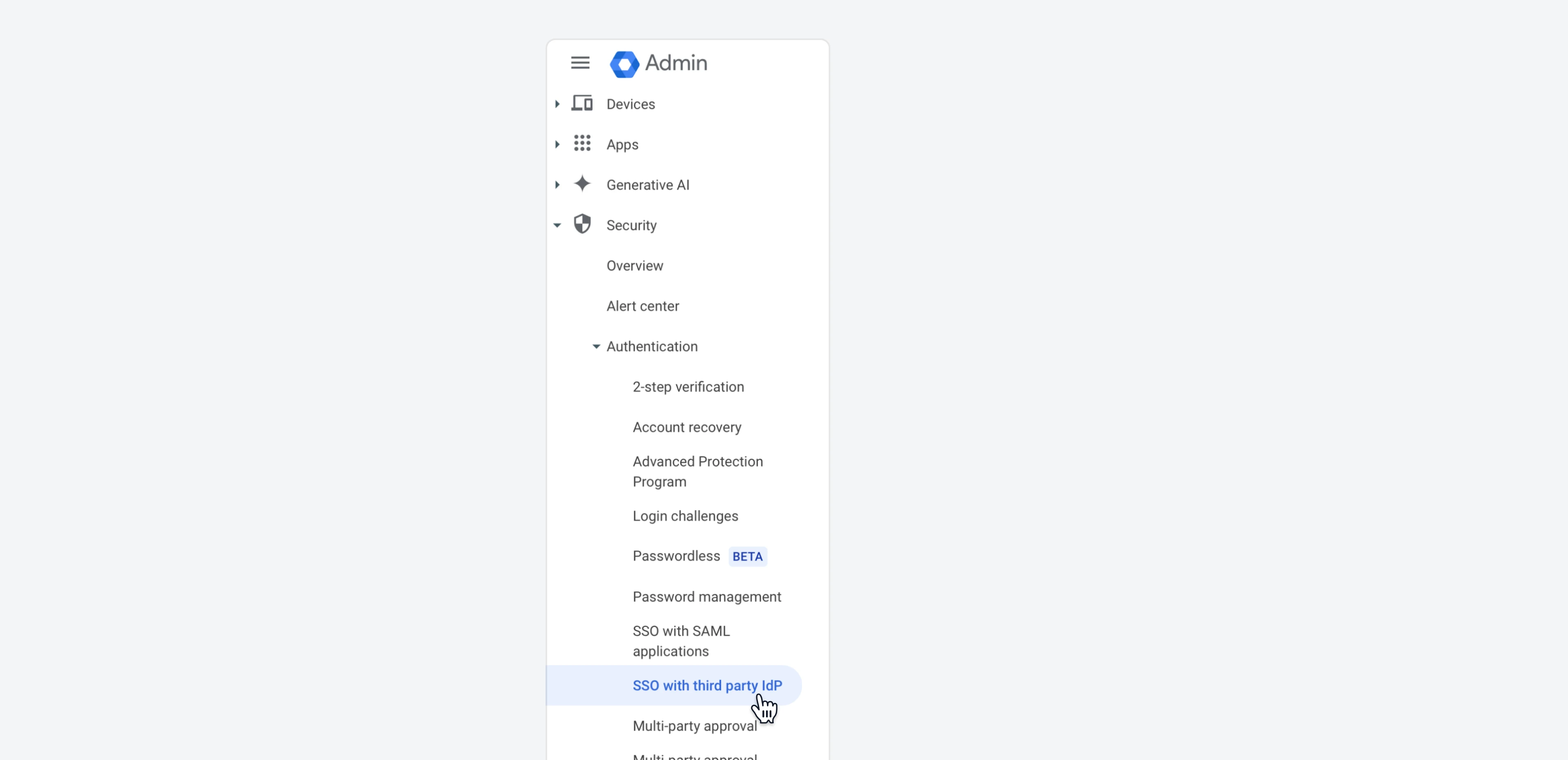
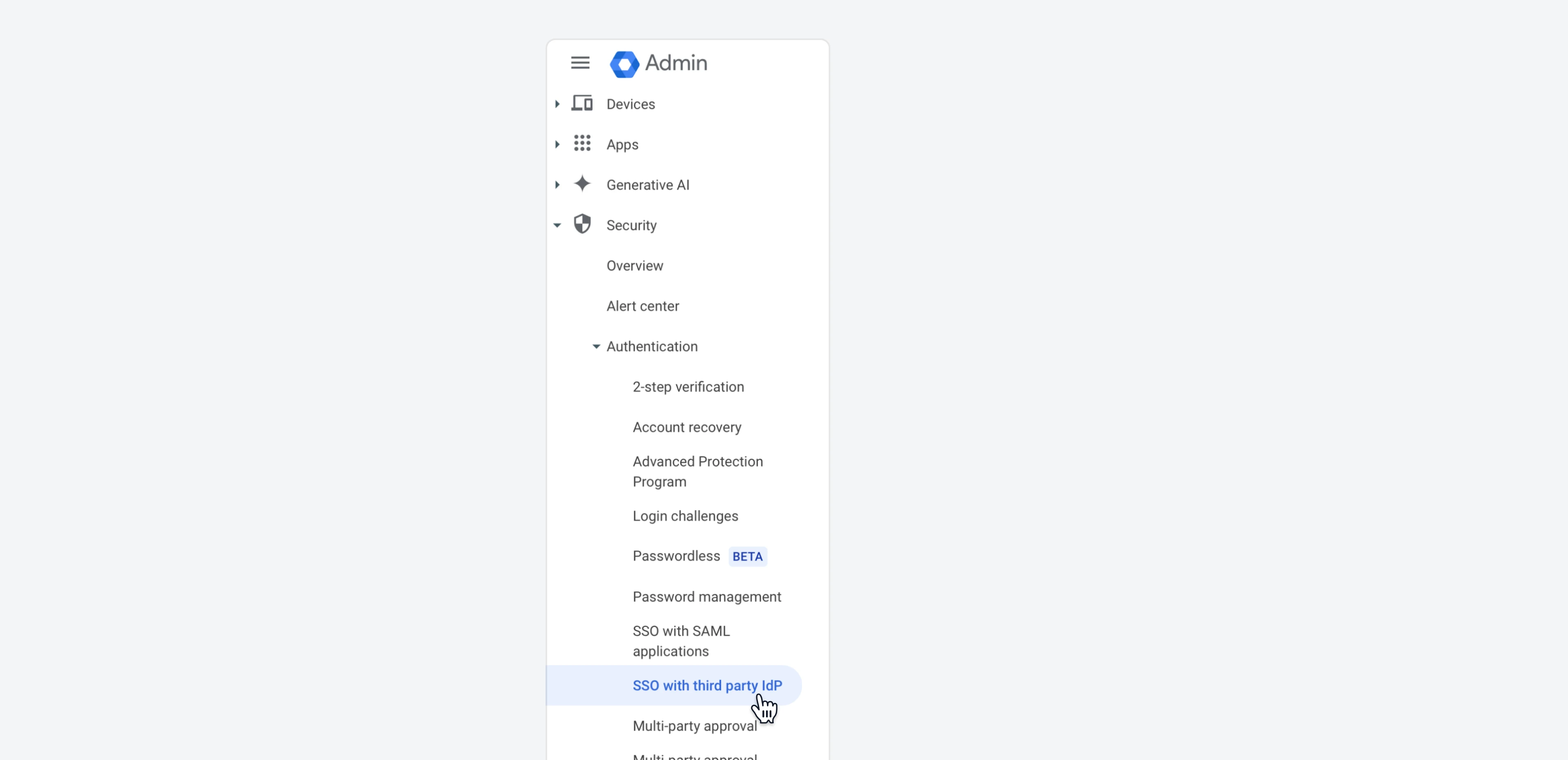
- On the left sidebar, go to
Security > Authentication > SSO with third party IdP.
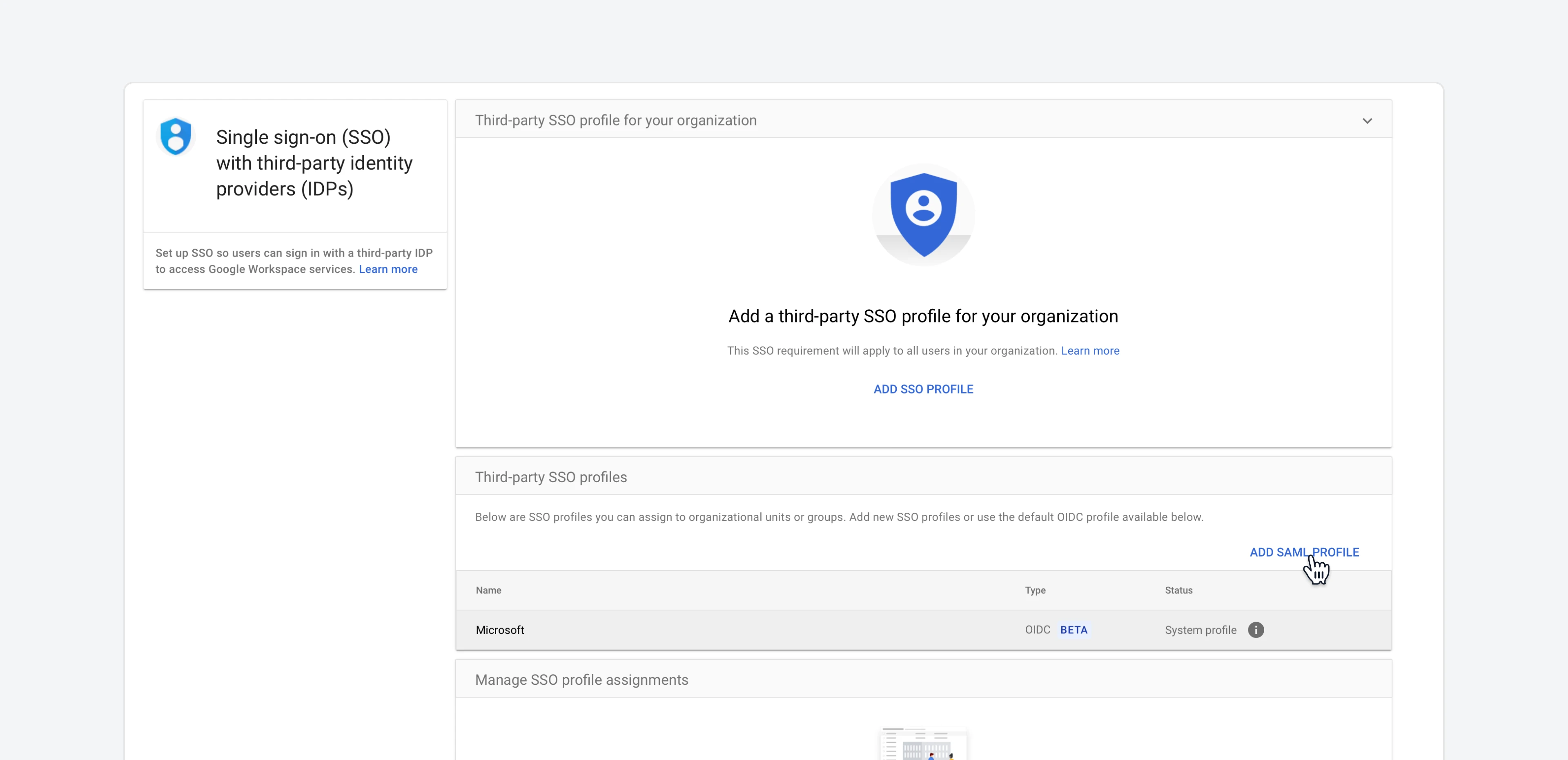
- On the
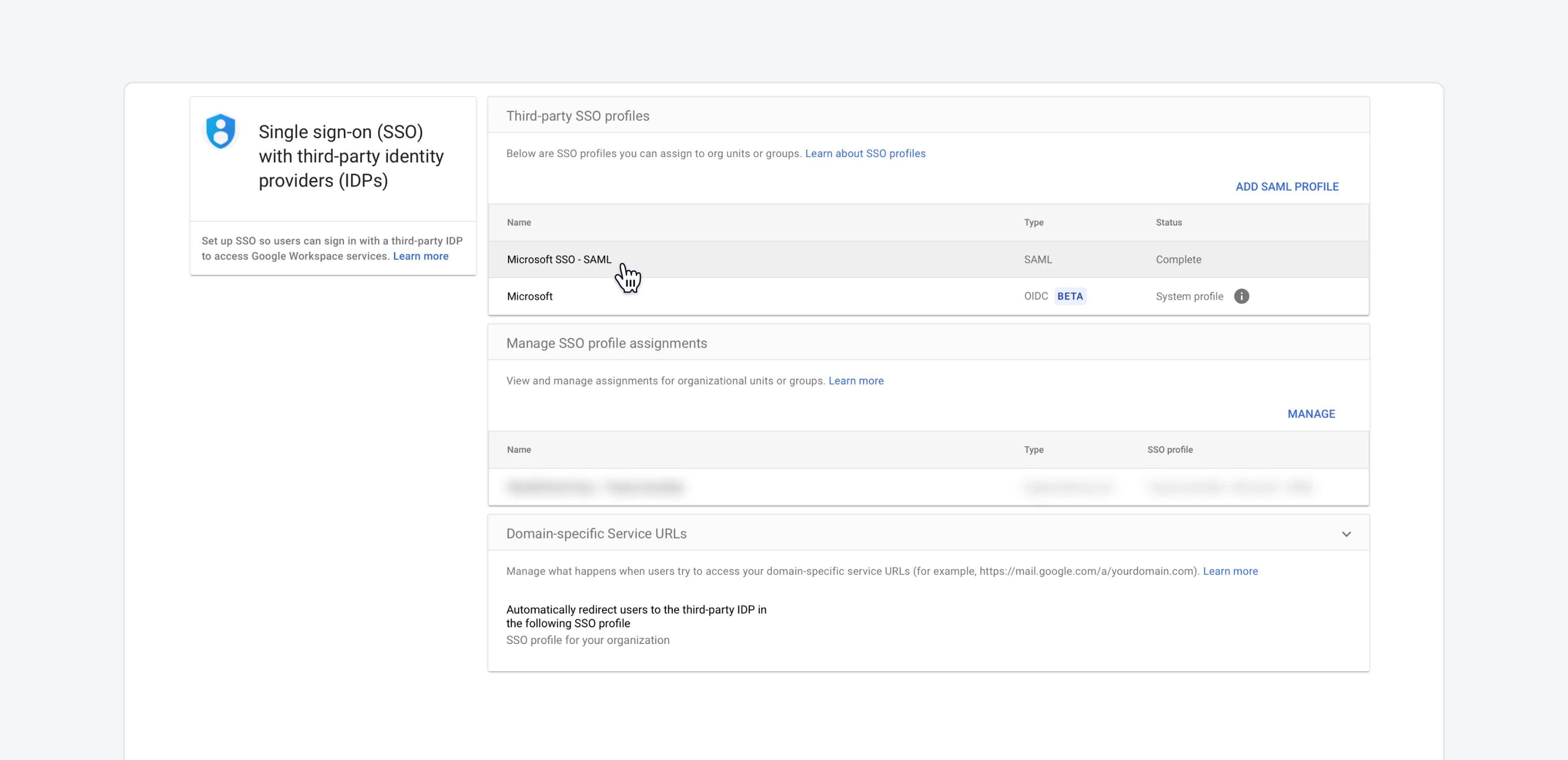
Third-party SSO profilessection, click onAdd SAML profile.
- A modal will open. There, you will need to input some information.
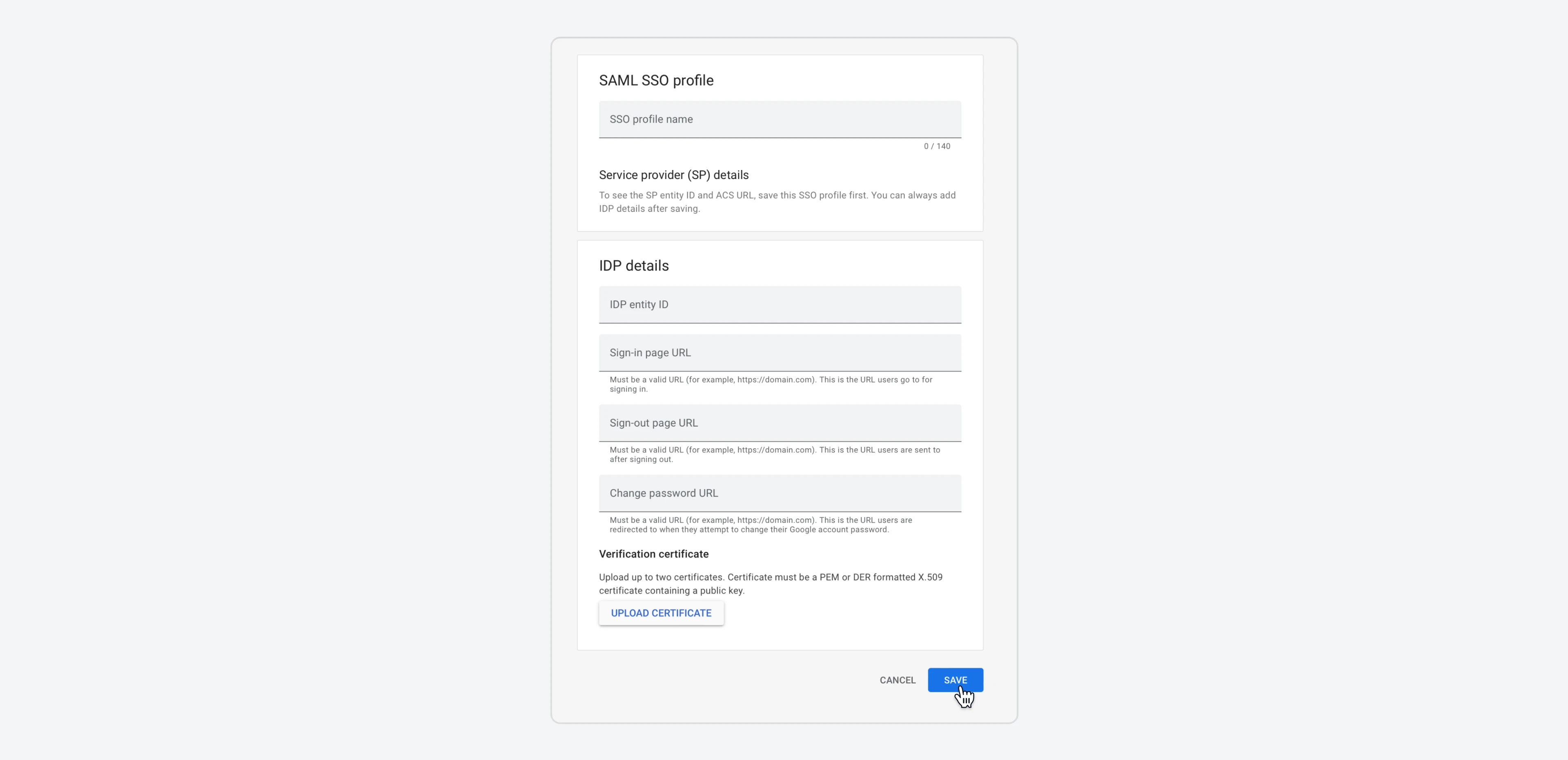
SSO profile name: typeMicrosoft SSO - SAML, or any naming of your choice.IDP entity ID: leave blank.Sign-in page URL: leave blank.Sign-out page URL: leave blank.Change password URL: leave blank.- Don’t update a verification certificate yet.
- Once everything is filled, click
Save. - The
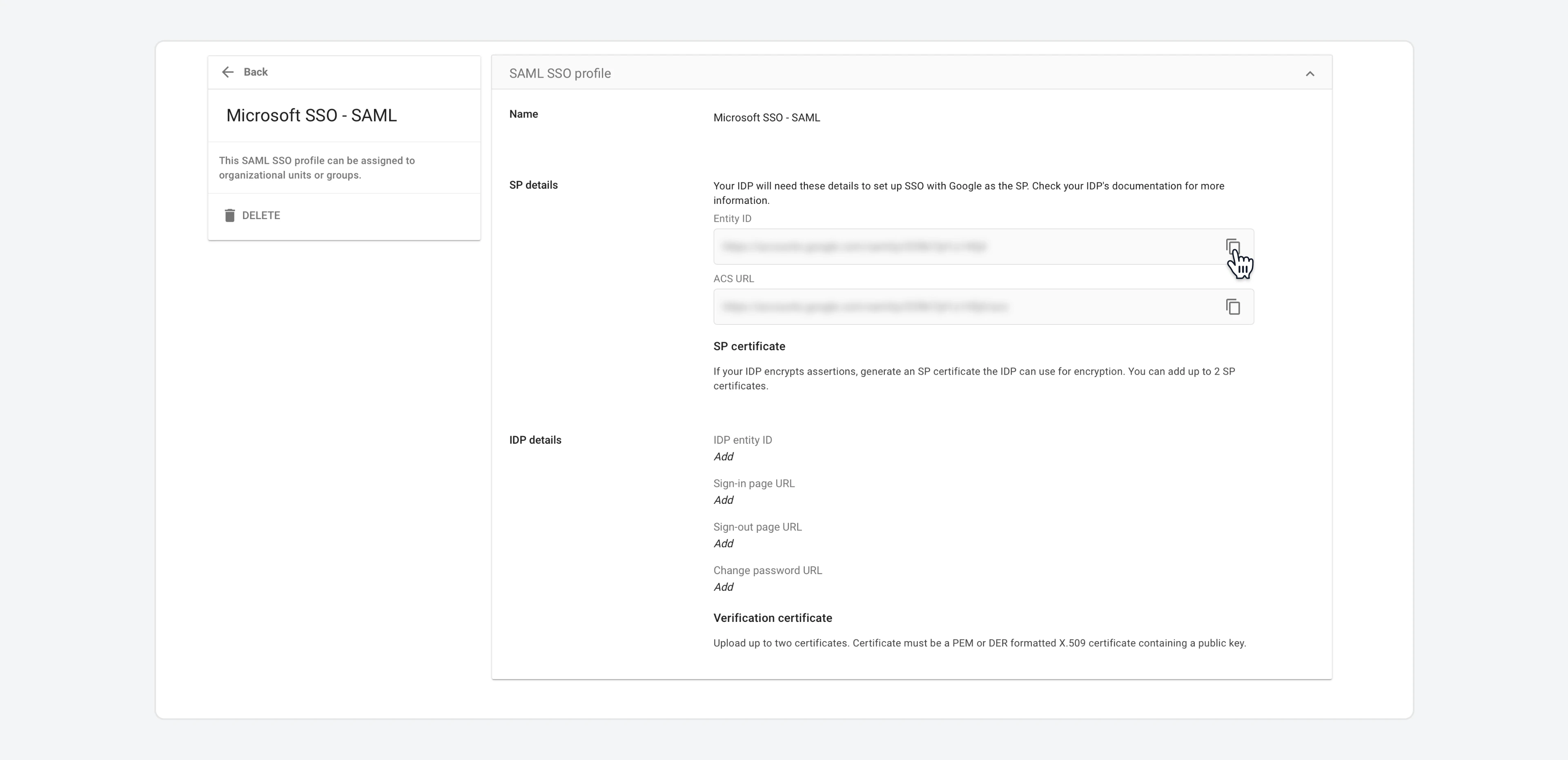
SAML SSO profilepage that appears contains two URLs (Entity IDandACS URL). Save these URLs, as you will need them in the next section when you configure Microsoft Entra ID.
Install the Google Cloud connector in Microsoft Entra ID
- Sign in to the Microsoft Entra admin center.
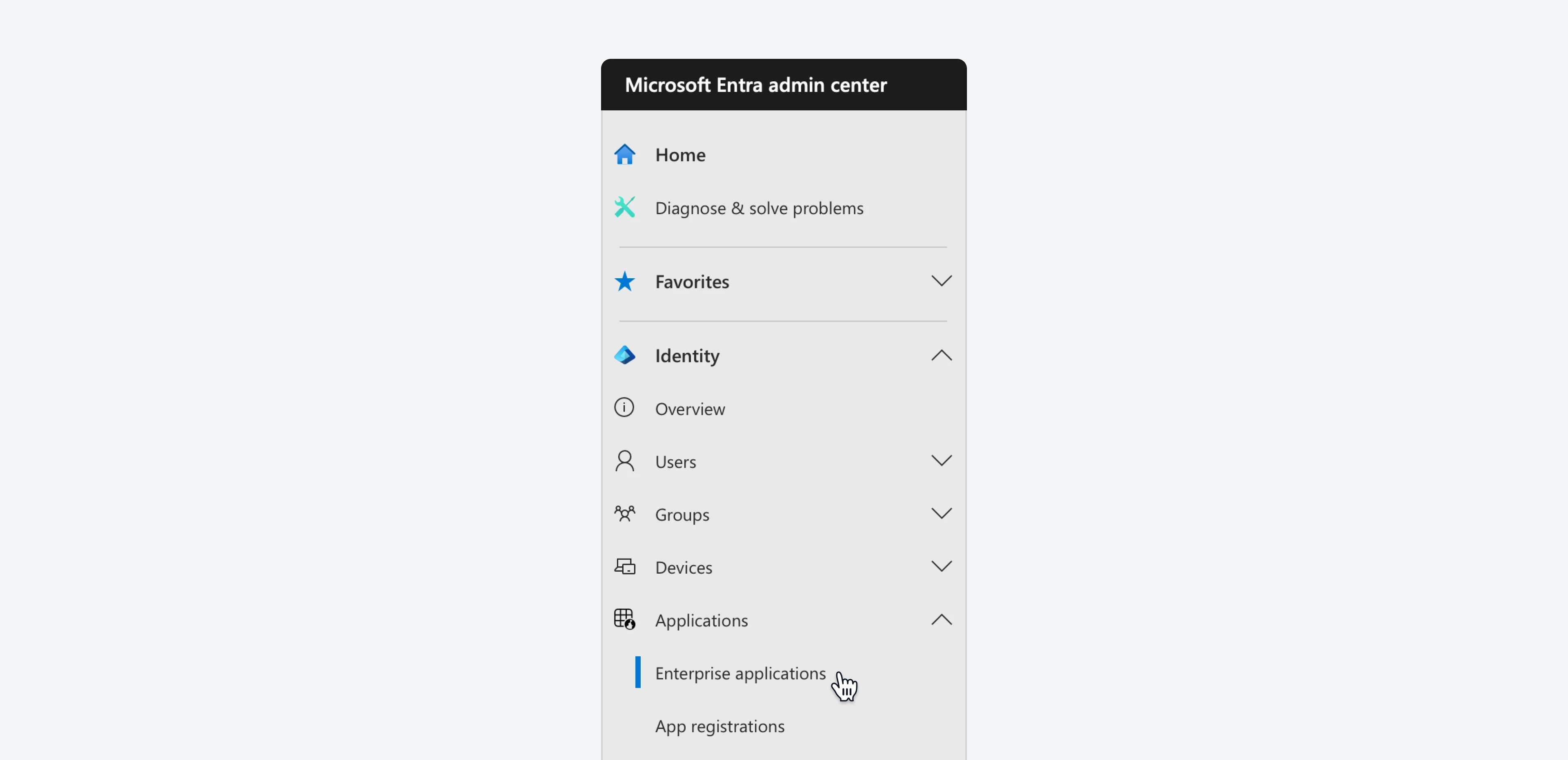
- Go to
Identity > Applications > Enterprise applicationsand then click onNew application.
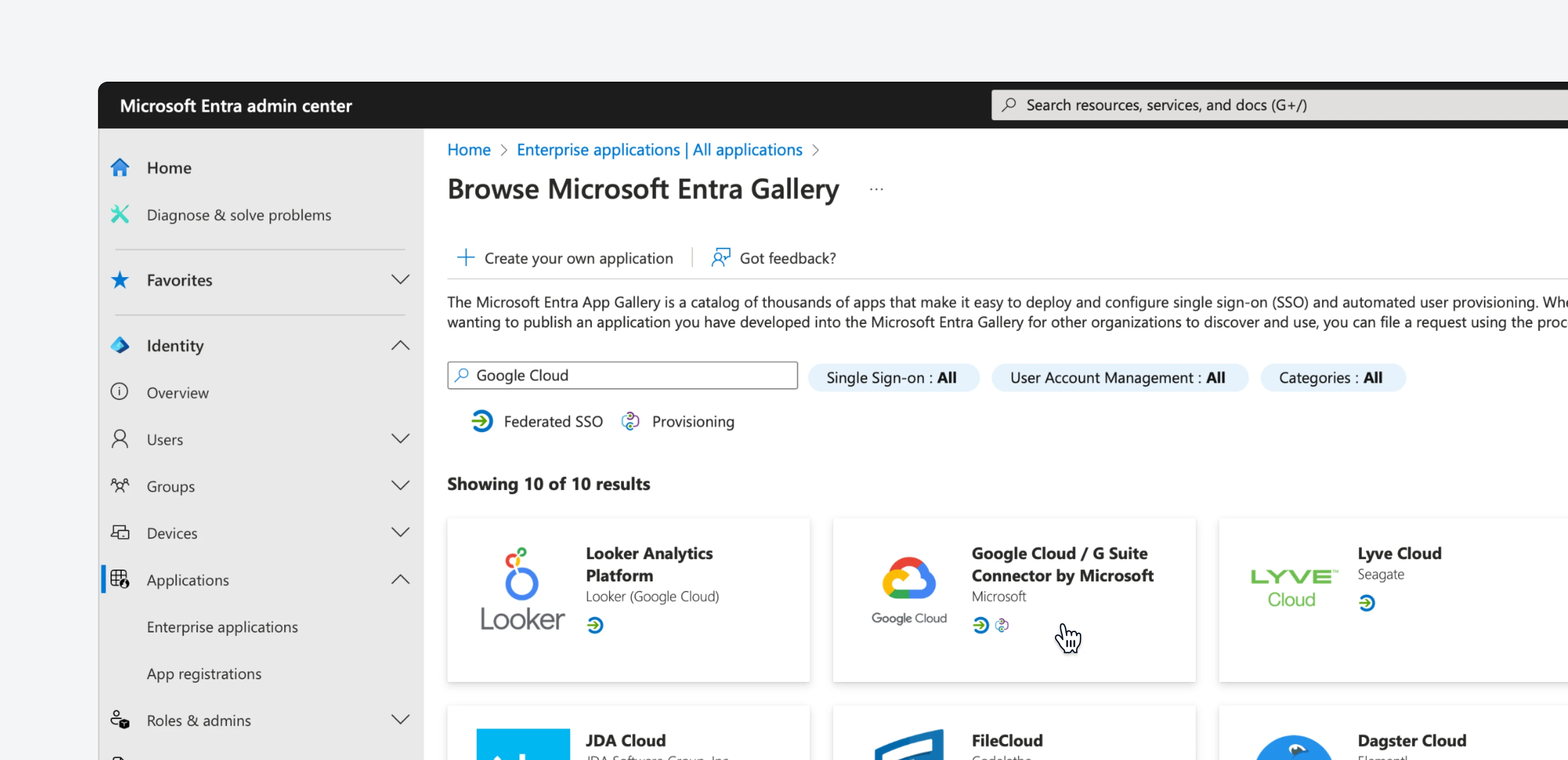
- In the search bar, type “Google Cloud”.
- Select
Google Cloud / G Suite Connector by Microsoftfrom the results. A drawer menu will appear on the left. Now, click on theCreatebutton to add the application.
- Wait a few seconds, and the application will be added to your tenant.
Set up Microsoft Entra SSO
Now, you need to establish a relationship between your users in Microsoft Entra and the related user in Google Cloud.- Sign in to the Microsoft Entra admin center.
- Go to
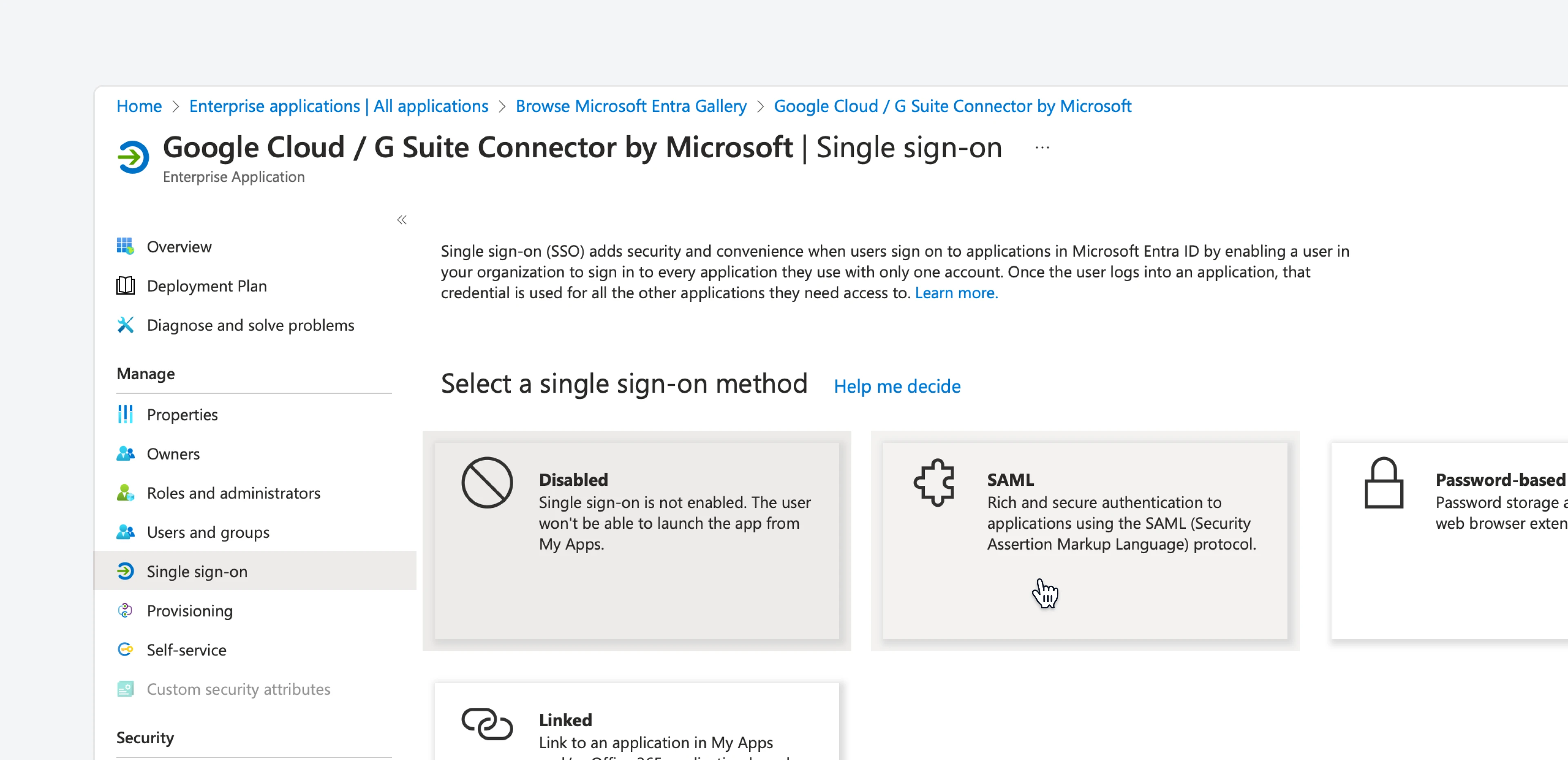
Identity > Applications > Enterprise applications > Google Cloud / G Suite Connector by Microsoft. There, go to theSingle-sign-onsection.
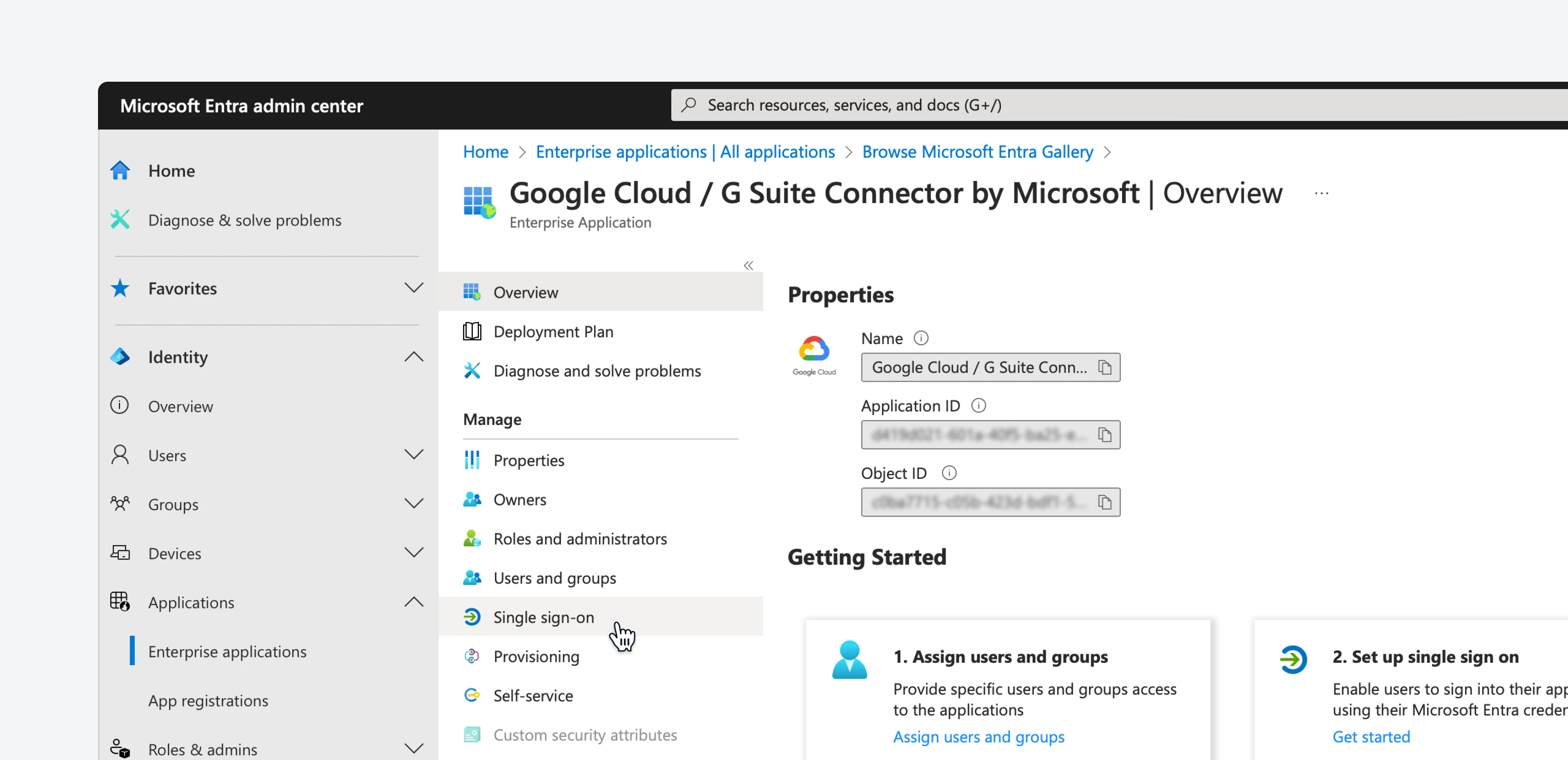
- Select the
SAMLoption.
- On the
Basic SAML Configurationsection, click on the pencil icon to edit the settings.
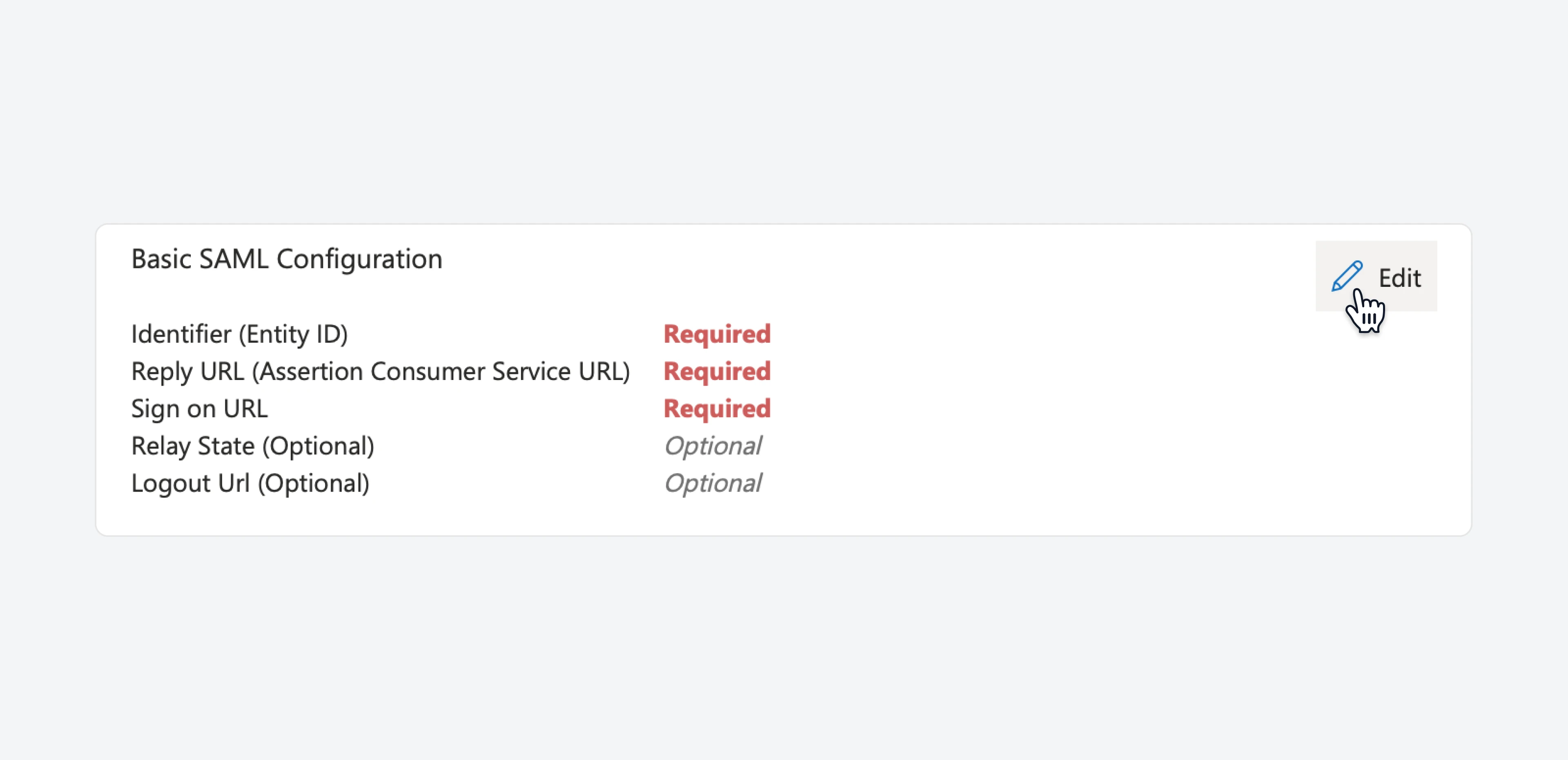
- In the
Identifiertextbox, paste theEntity IDthat you saved previously from the Google admin, and setDefaulttoenabled. Remove all other entries. - In the
Reply URLtextbox, paste theACS URLthat you saved previously from the Google admin. - In the
Sign on URLtextbox, paste the custom URL that the Email Meter team has provided to you. If you don’t have it, please get in touch with your point of contact. - Then, click
Saveto save your changes. - On the
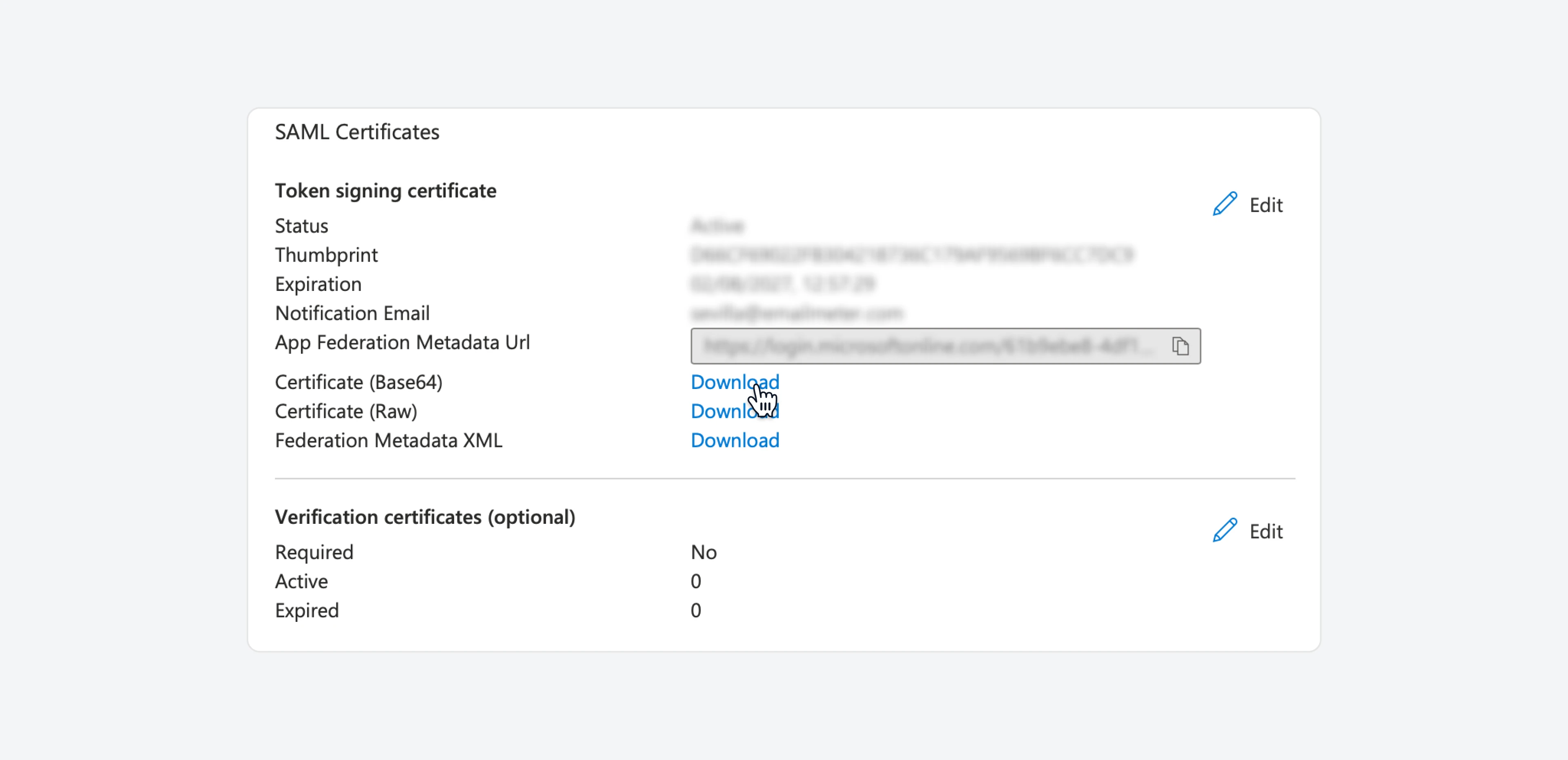
SAML Signing Certificatesection, findCertificate (Base 64)and clickDownloadto download the certificate. You will need it shortly.
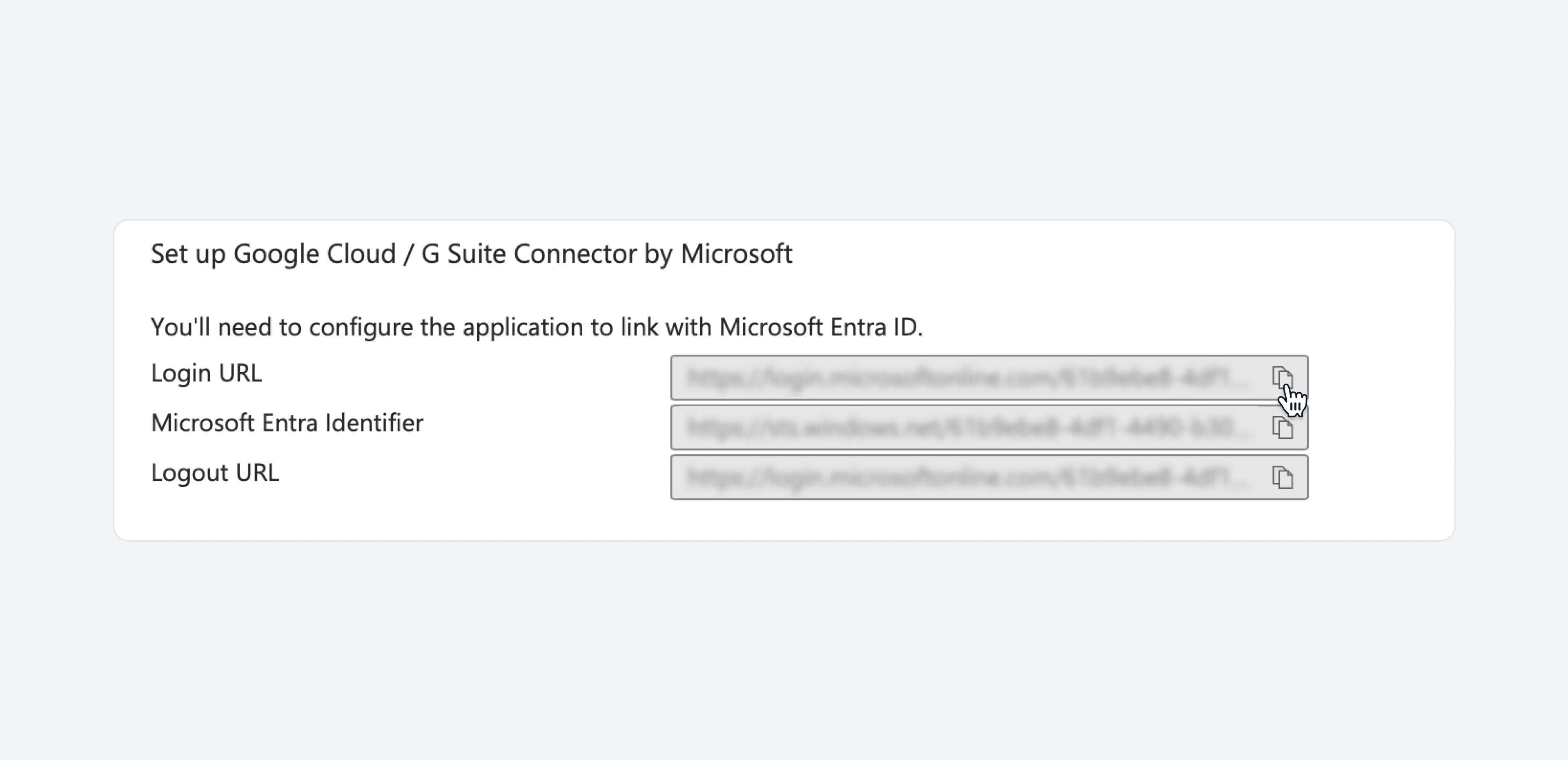
- On the
Set up Google Cloud / G Suite Connector by Microsoftsection, copy the three URLs and save them, as we will need them to set everything up in Google Cloud. Alternatively, leave this tab open so you can go back to it quickly.
Complete the SAML profile
- Return to the Google Admin console, and go to
Security > Authentication > SSO with third party IdP.
- Open the
Microsoft SSO - SAMLprofile that you created earlier.
-
Click the
IDP detailssection to edit the settings.- In the
IDP entity IDfield, paste the value ofMicrosoft Entra Identifierfrom the previous section. - In the
Sign-in page URLfield, paste the value ofLogin URLfrom the previous section. - In the
Sign-out page URLfield, enter the following URL:
Change password URL- In the
Change password URL, enter the following URL:
Change password URL- In the
Verification certificatesection, update the certificate that you downloaded previously. - Once everything is filled, click
Save.
- In the
Assign the SAML profile
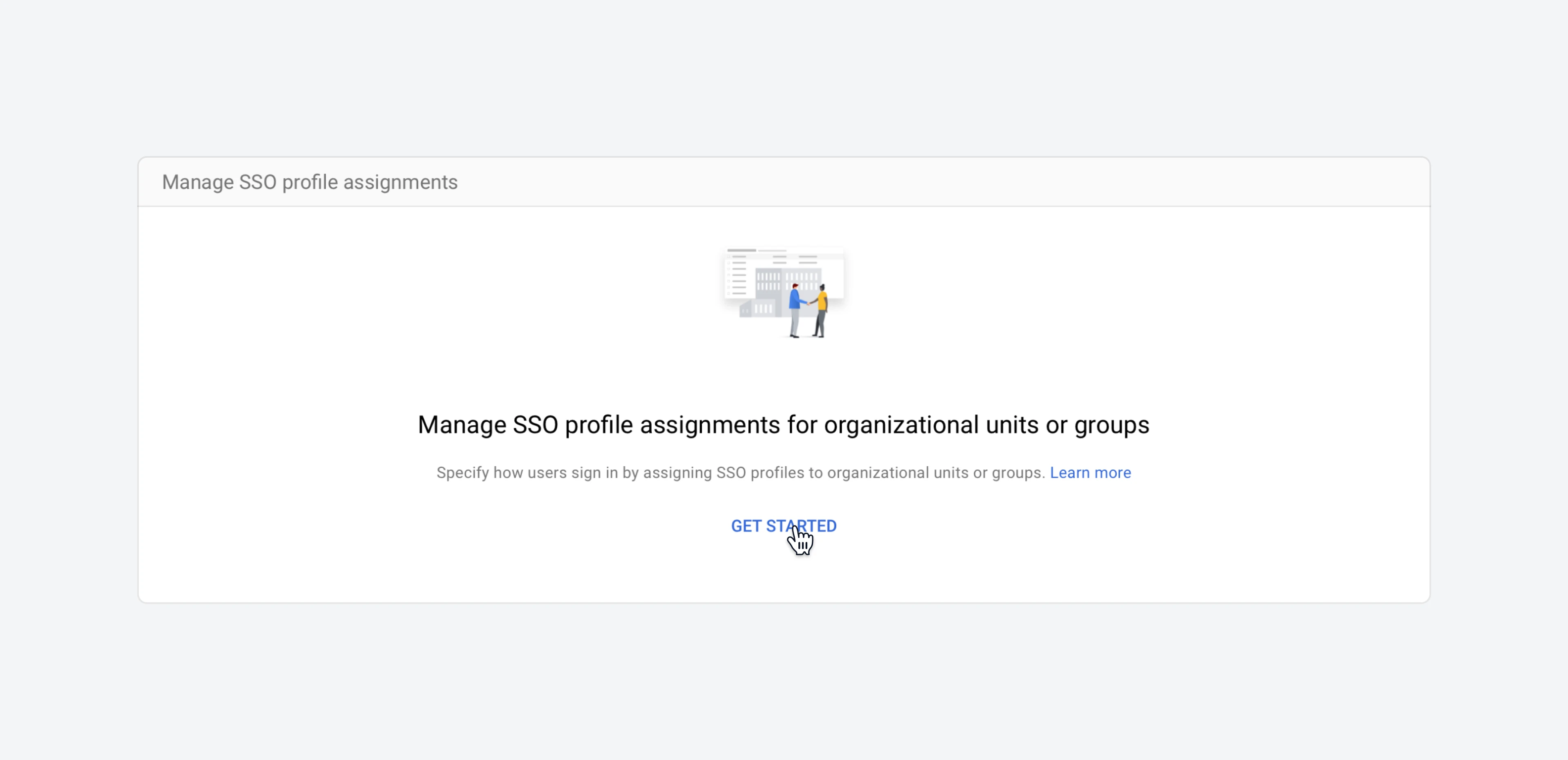
- On the
Manage SSO profile assignementssection, click onGet started.
- On the
SSO profile assignement, clickAnother SSO profileand select the one you’ve created in the past step. If you’ve followed our recommended naming conventions, it will be calledMicrosoft SSO - SAML.
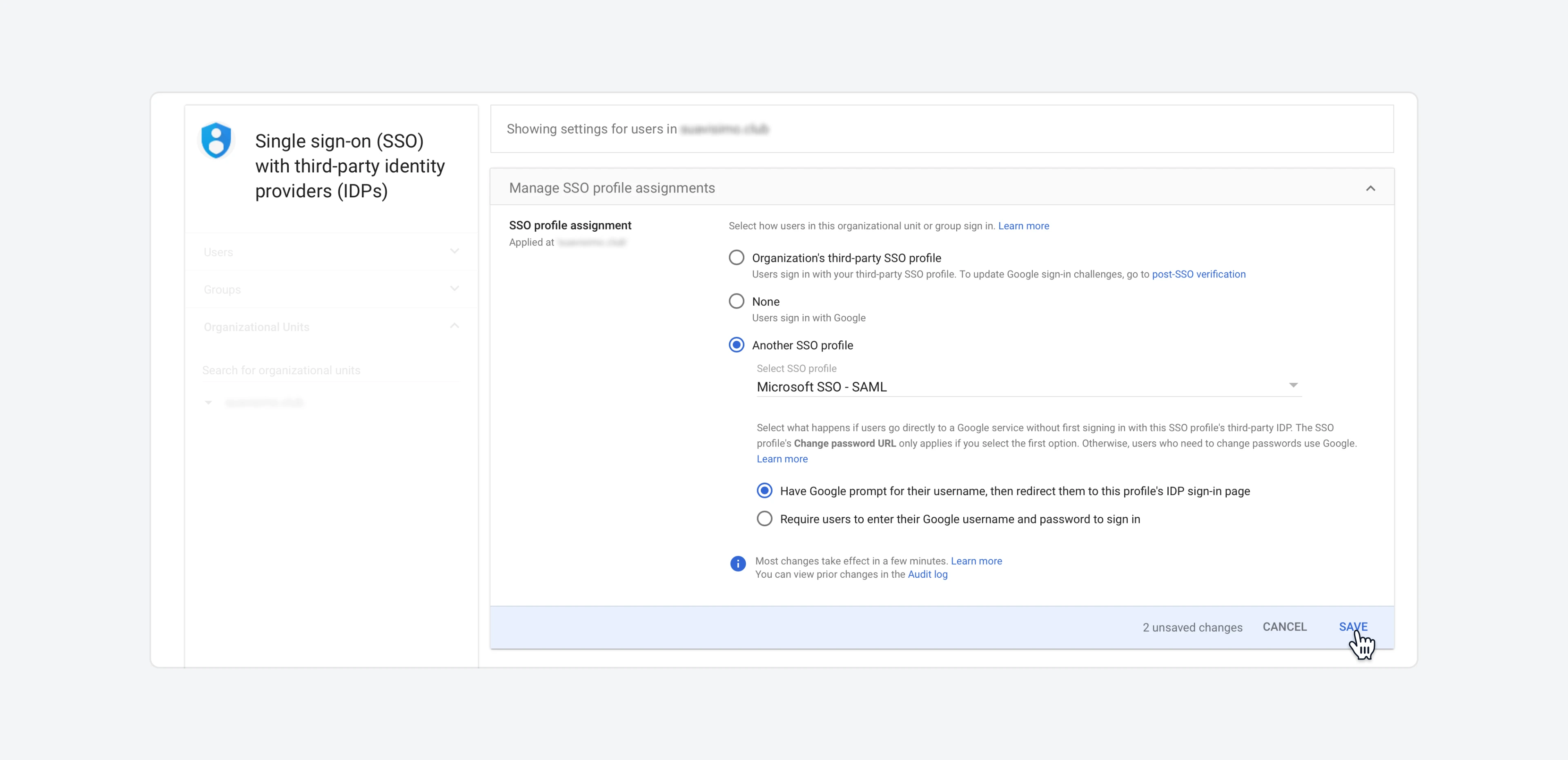
- Click
Save.
Assign users
On Microsoft’s side
To enable users to use single sign-on in Google with their Microsoft SSO, you need to grant them access to the Google Cloud / G Suite Connector by Microsoft.- Sign in to the Microsoft Entra admin center.
- Go to
Identity > Applications > Enterprise applications > Google Cloud / G Suite Connector by Microsoft. There, go to theUsers and groupssection.
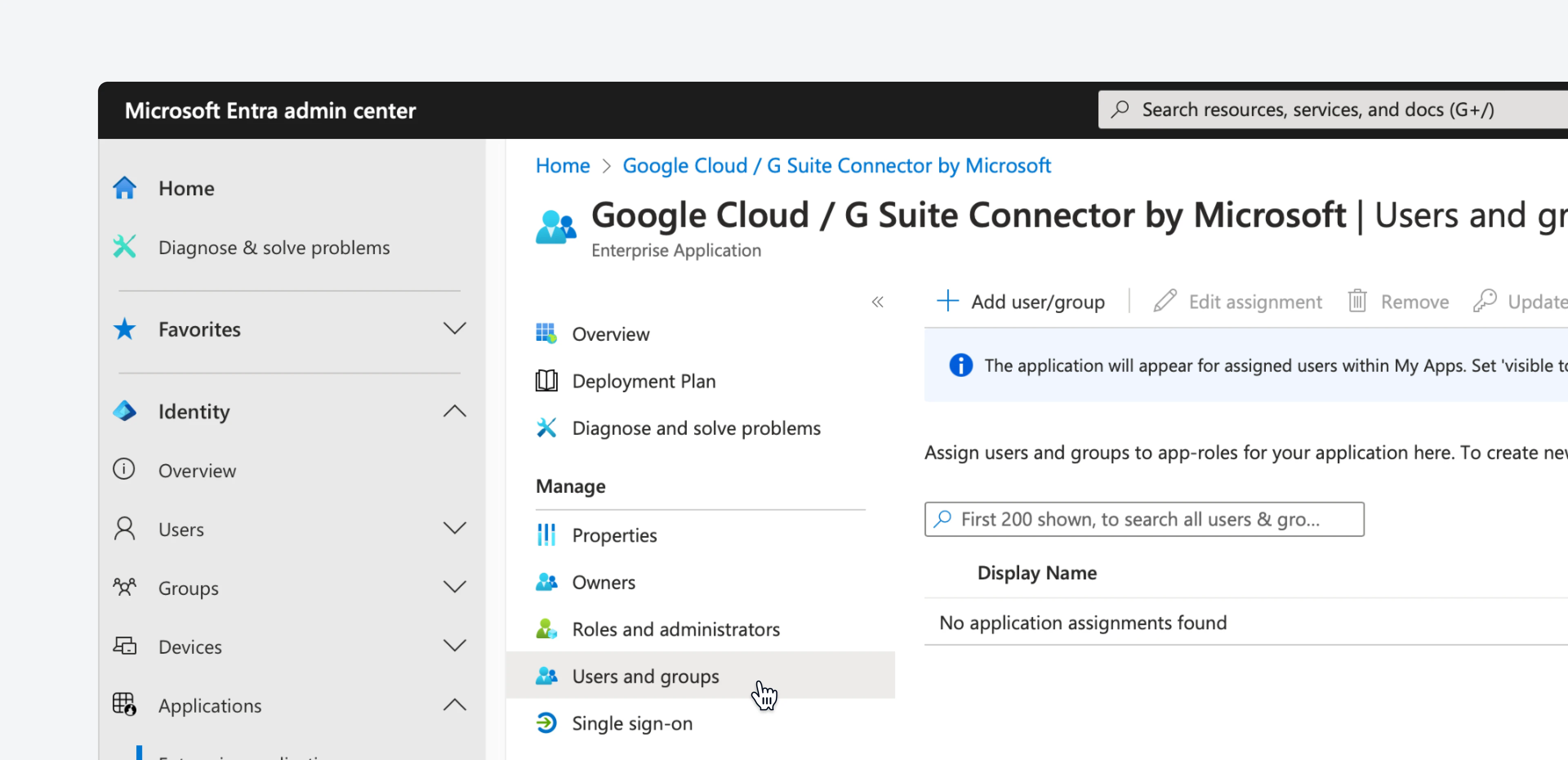
- Click on
Add user/group, and then select the users and/or groups that you need.
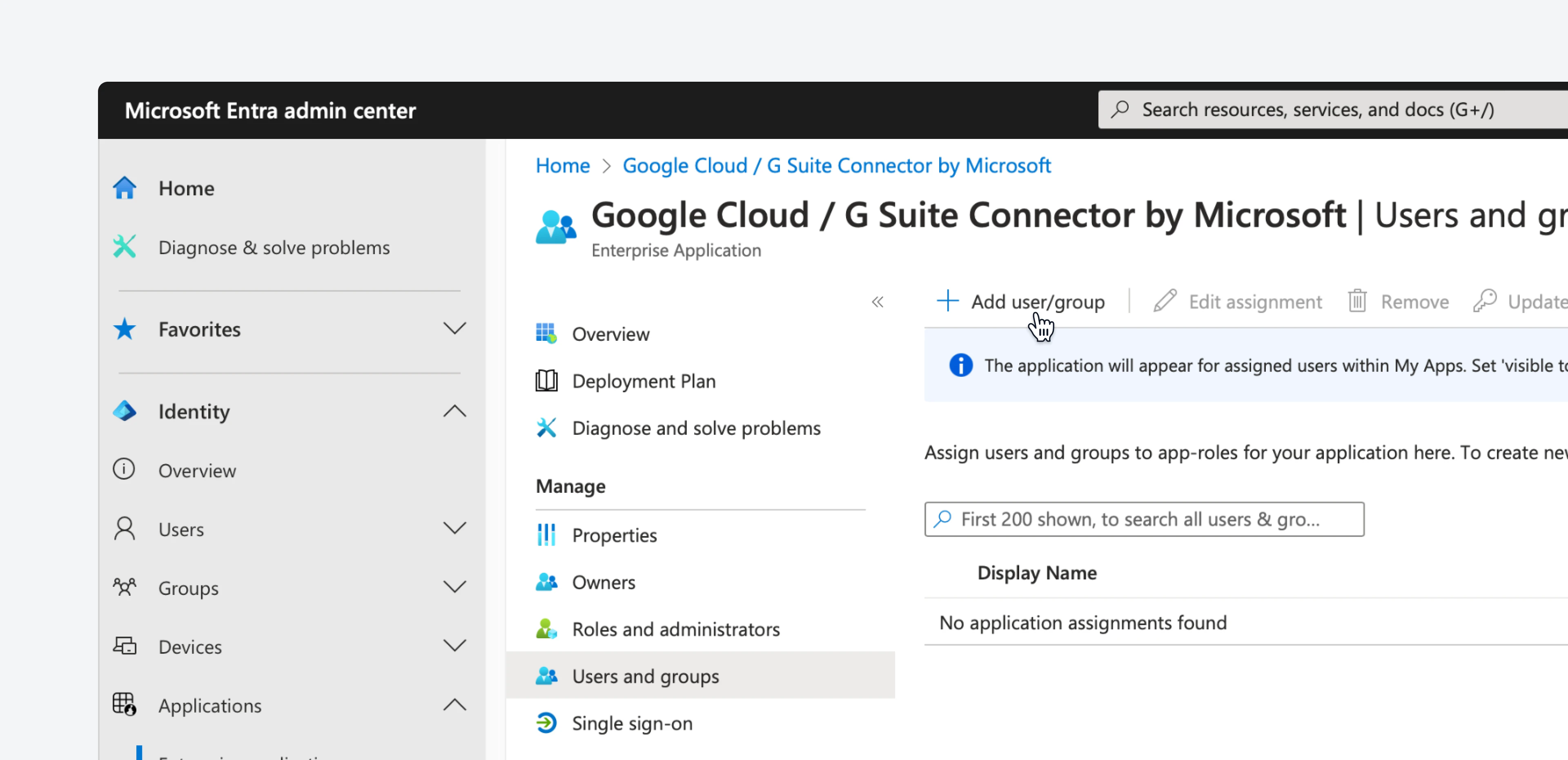
- Once you’re done, click on the
Assignbutton.
On Google’s side
In order for this to work, the user needs to exist in both Google and Microsoft. If you don’t want to manually create users in Google when needed, you can also configure automatic user provisioning following Microsoft’s or Google’s documentation.Test SSO
If you’ve followed this steps correctly, your users will now be able to login to Google services using their existing Microsoft SSO. To test this, click this link. It will redirect you to the Google login flow. After inputting your email address, it will redirect you to Microsoft to complete the login process.Frequently asked questions
Can I enable single sign-on only for a subset of my users?
Can I enable single sign-on only for a subset of my users?
Yes, the SSO profiles can be selected per User, Organizational Unit or Group in the Google Workspace end. Only the users or groups you select will be redirected to Microsoft Entra ID for login.
Do I need to pay for each Google user?
Do I need to pay for each Google user?
No, you do not need to pay for each Google user. Google Cloud Identity accounts are sufficient for accessing Google services, so a Google Workspace license is not required. By default, Google assigns a Google Workspace paid license to new users, but you can disable automatic licensing by following this guide.